Traditional security controls are insufficient to protect from cyberattacks in the digital domain, compelling organizations to adopt a Zero Trust Network. The principles are simple – trust no user or device, inside or outside the private network, cloud network, and grant as little access as possible upon reliable identification.
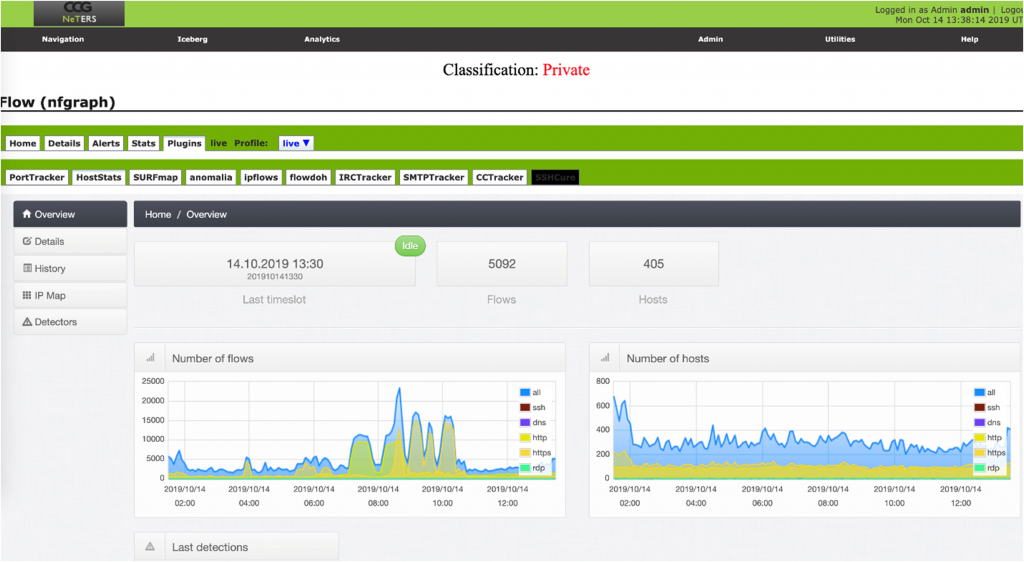
But one of the issues facing network security monitoring tools is that they only generate alerts; often good alerts. Usually, an event will display the source IP address (the system that caused the event), destination IP address (the system that was targeted), event description, and a priority rating. However, at times organizations need more than just an alert to fix problems on a network. Other pieces of metadata can be just as critical as the alert itself. Examples include:
- What inbound and outbound network connections were active to the destination IP address at the time the event was triggered?
- Were there any other events associated with the destination IP address?
- What DNS queries were associated with the destination IP address?
- If the source IP address is on the LAN, is there any unusual activity associated with it (items 1 to 3 above)?
CCG’s CheckMate is ready to take on this task for you, providing your company with 24/7 Cyber Security monitoring by adopting a Zero Trust Network as part of our complete Cyber Security strategy. CheckMate will maintain the health of your system and monitor its performance to detect any abnormalities the moment they occur and stop problems immediately.
To learn more about CCG’s CheckMate latest Artificial Intelligent software product that will protect your network from cyber-crime, visit our website at https://www.phen-ai.com.