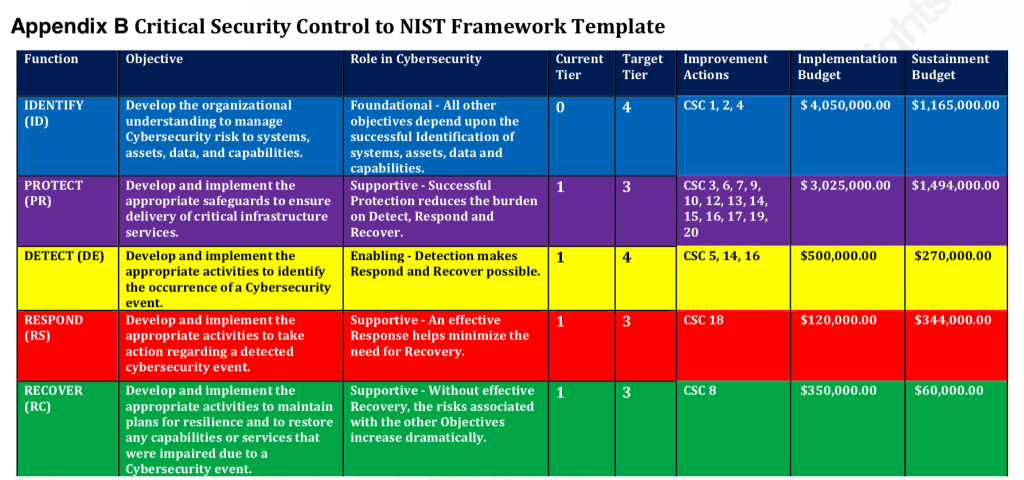
National Institute of Standards and Technology (NIST) developed a Cybersecurity framework which enables businesses have an understanding of cyber risks and how these businesses can protect themselves.These 5 functions are not only applicable to cybersecurity risk management, but also to risk management at large.
Canfield Cyberdefense Group (CCG) adopts the NIST framework to develop solutions that provides auditing that follows various leading standards for compliance (NIST, PCI-DSS, CAESARS) and ensures configuration checks and settings comply with industry standards (NIST, DISA-STIG, SCAP)
▪ Identify:
CCG security solution utilizes a lighter level packet inspection vs a traditional IDS, to provide an array of low-cost sensors to enable seeing all activities and actions inside the network. NeTERS has the ability to tag, collect, trace and inspect media documents, file documents, web code, and applications in transit, and identifies where various files have moved through the network. NeTERS can also track viruses and virus paths, identifying which systems have been infected
▪ Protect:
Provides a log repository from many different systems; it is able to make correlations between logs that were never before available. This solution provides the security necessary to guard and protect these key information assets. Our threat analyzer (a component of SLA) provides a mechanism to explore and use business intelligence techniques to ferret out relationships among the data sets to further identify strengths, weaknesses, and vulnerabilities.
▪ Detect
NeTERS, this solution provides a higher collection and view of the network’s activities, objects, and evolution, IE: ‘weather patterns.’ Providing system and application data paths throughout the customer’s network. We utilize a lighter level packet inspection vs a traditional IDS, to provide an array of low-cost sensors to enable seeing all activities and actions inside the network. NeTERS works in conjunction with existing IDSs or can provide those capabilities within NeTERS
▪ Respond:
CanSecure solution contains patent-pending technology providing the ability to detect and manage known vulnerabilities as well as use fuzzing to detect anomalies and penetrate systems with new and unknown flaws. It uses well known suggested settings and configurations from NIST, DISA, and others to ensure systems are configured to be as secure as possible.
▪ Recover
In the case where there is an attack, NIST requires an organization to reconstruct/regulate the system and part of the network that was affected. image below shows mapping graphic for the cost to implement compliance.
In the event of cybersecurity attack, CCG will suggest interested parties to get complete coverage, at fraction of the cost by having an integrated system driven by humanoid AI. We use NIST CPEs to reduce 99.9% of surface area weaknesses.